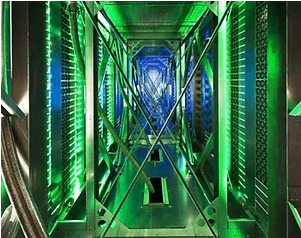
Data Center Management
with RFID
Automate the quality of service, security, and compliance that are crucial to data centers.
RFID has become an integral part of data center management, offering numerous benefits in tracking and optimizing critical infrastructure operations.
RFID systems are replacing manual barcode tracking and Excel lists and help automate the quality of service, security, and compliance that are crucial to data center operations.
Data center asset management relies on RFID to track and manage assets with precision.

Each piece of equipment, from servers and switches to storage devices, networking equipment, rack PDUs, patch panels… can be tagged with RFID chips.
This allows for real-time monitoring of asset locations, reducing the risk of equipment loss or theft. Operators can quickly locate and automatically manage assets, leading to improved inventory accuracy and reduced downtime due to equipment unavailability.
RFID data can be used to track the maintenance history and full lifecycle of equipment, from reception of RFID-enabled devices directly from the vendor, to commissioning, maintenance, and eventually disposal. This information helps data center managers schedule preventive maintenance and plan for equipment replacements, ensuring that critical components are always in optimal working condition.
The size of a typical data center has multiplied, so has the number of equipment, components and spare parts in its inventory.

RFID technology streamlines inventory management by automating the tracking of items as they are used and restocked. This reduces manual record-keeping errors and helps data centers maintain optimal levels of spare parts, reducing the risk of equipment failures due to component shortages.
Data centers often need to comply with regulatory requirements (for instance: ISO/IEC 27001 for information security, Sarbanes-Oxley, the HITECH Act, PCI, HIPAA…) and undergo audits.
RFID technology enables faster and more accurate data center audits by automating data center management. Physical audits can be performed more regularly and standardized across multiple locations, to offer real-time operational visibility. RFID systems provide a reliable and automated way to track equipment and access logs, simplifying the compliance process and reducing the risk of compliance-related issues.
Data center infrastructure management (DCIM) sits at the intersection of IT and facilities management.
Its goal is to provide situational awareness to a data center manager when it comes to performance, so that energy, equipment and floor space are used as efficiently as possible.
RFID-based access control systems are well known and enhance data center security. Authorized personnel can be issued RFID cards or badges, which are required for entry to secure areas. This minimizes unauthorized access and ensures that only qualified personnel can enter sensitive parts of the data center.
RFID solutions help data centers become more sustainable with real-time monitoring and energy management.
Temperature and humidity levels are critical factors in data center operation. RFID sensors can be used to monitor environmental conditions in real-time. If conditions deviate from the specified range, alerts can be triggered, allowing data center managers to take immediate corrective actions to prevent equipment overheating or damage.
RFID technology can also contribute to energy efficiency in data centers. By tracking the location and usage of equipment, data center managers can identify underutilized or idle assets and make informed decisions about their power usage. This can lead to significant energy savings.
Case Studies RFID Data Centers
RFID For Data Centers
99% Asset Location Accuracy
Real-time location tracking of assets with RFID within the data center.
Up to 100% Equipment Availability
Leveraging RFID-enabled situational awareness to maximize equipment uptime by proactively scheduling maintenance and replacements.
Compliance Readiness
Ensuring data center's continuous readiness for audits with a high compliance score and minimal audit findings.
FAQs RFID Data Centers
Asset Tracking Automation in Data Centers
Automation Technology
Data centers come in high-density configurations, with equipment in small and large sizes.
Tracking and identification technologies that can be automated, ie work in bulk, without having to pull servers out of their racks.
Interoperability
With ITAM systems such as Nlyte, ServiceNow, Remedy...
Machines and Humans
A best practice that requires printing and encoding on-site or at point-of-manufacture.
Unique Identifier
Identification, traceability, compliance reporting at item-level.
RFID Systems For Data Center Management
Tracking
Handheld readers are best suited for flexible, on-the-spot, mobile checks, such as scanning a facility without having to remove any item, or identifying misplaced equipment.
Monitoring
Fixed readers can be adapted onto server cabinets to automate real-time visibility at the rack level.
RFID INTEGRATION
Some ITAM systems facilitate RFID integration by providing native support.
Embedded
Data center OEMs such as Cisco and Intel offer equipment that embed RFID to enable tracking features from cradle to grave.
RFID Tags for Data Centers
- Data centers are metal-dense environments: RFID tags and labels are available that can be custom-tuned to minimize cross-reads and interferences.
- Unique identifier with serialized ID (TID) or custom encoding of User and EPC memories.
- Identification information can be printed and encoded, to make it readable by both machines and people.
Xerafy has RFID tagging solutions that meet industry standards and are specifically engineered for data centers.
Available for both retrofit and source-tagging, the award-winning Xerafy RFID Tags and Labels are designed to deliver optimal performance for data center assets, be they used on or in metal, and on plastics.
Compact form factors are available to fit blade servers, rack locations, and mobile devices. More options are available regarding chip memory, materials, and mounting options.
Can RFID Be Used For Data Center Environmental Monitoring?
Yes, passive RFID sensors such as the Xerafy Xense series are available to monitor parameters such as temperature and moisture.
The process of monitoring environmental factors such as temperature, humidity, and water in data centers is known as data center environmental monitoring. It enables data center operators to become aware of any environmental hazards within the facility and take proactive measures to reduce their impact.